- Activant's Greene Street Observer
- Posts
- Authenticating AI Agents
Authenticating AI Agents
The Next Big Identity Crisis in Cybersecurity

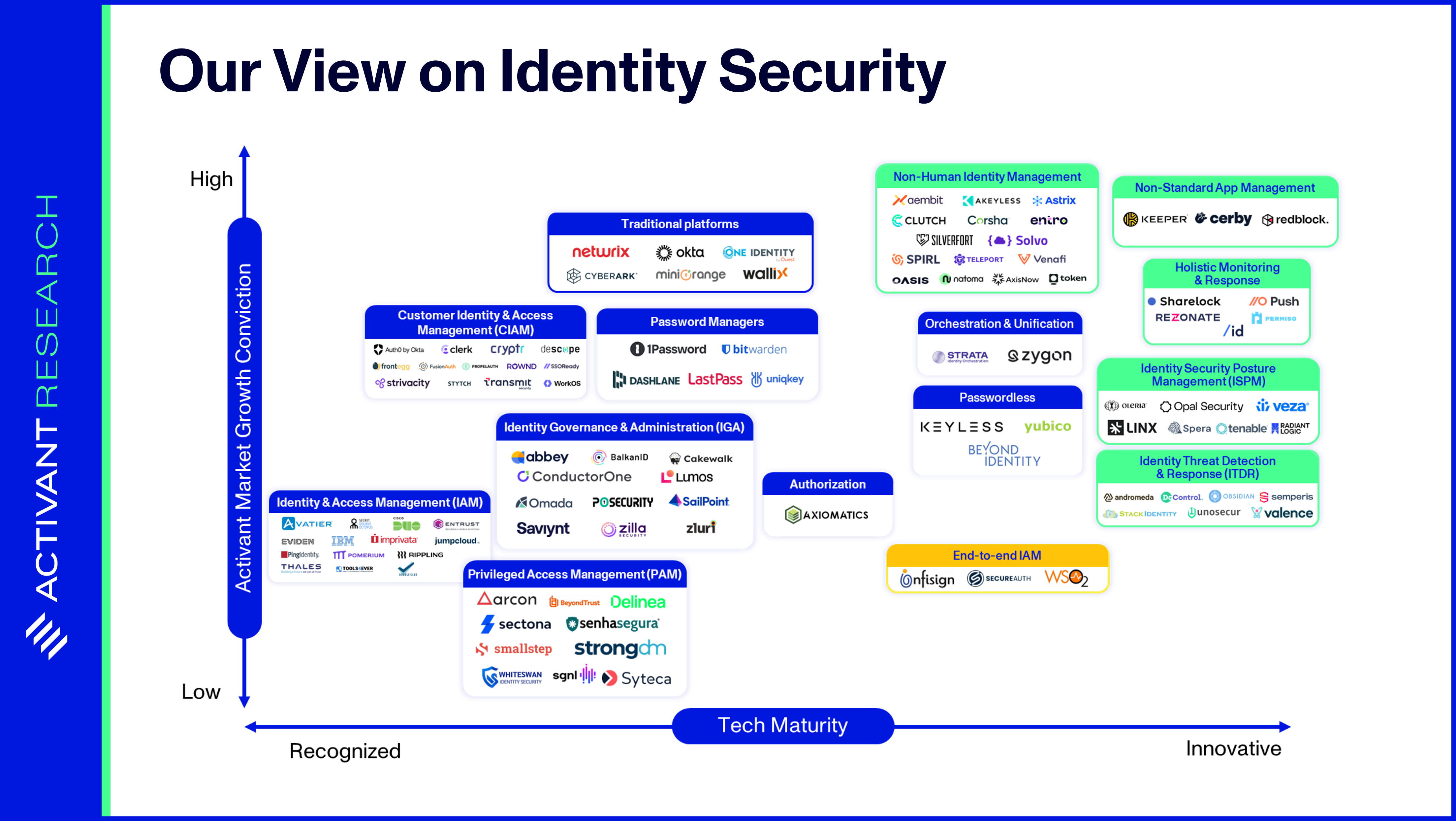
Knowledge work, such a critical piece of the modern economy, is increasingly executed via software applications. Humans access these applications and their underlying data using credentials, like a username/password pair. Identity Security, a $76bn market, has been established to secure these human identities. However, increasingly large swaths of today’s work are not done by humans, but by software.
Cloud workloads automatically provision new infrastructure and test and deploy code; software applications automate business processes such as payroll calculations; and bots execute trades in financial markets. Just like humans, these applications can’t have uncontrolled access to enterprise resources. We need non-human identities (NHIs) like API keys, X.509 certificates, and OAuth tokens to control which machine entities access specific data, and under which circumstances. Think of it as identity and access management (IAM) for machines.
However, as covered in our recent article, non-human identities are difficult to secure and quickly becoming a key attack vector. Fifty-five percent of organizations have experienced a breach or incident via their software supply chain that exploited vulnerabilities in NHIs. Driven by cloud adoption, business processes automation and a shift to microservices architectures, NHIs are growing at a rapid rate of ~2.5x every year, outnumbering human identities by a factor of 45x. Yet, the amount spent on NHI security is only 5%–10% of the $76bn spent on human identity security. If that sounds concerning, consider this: enterprises are racing to adopt AI agents, and soon every SaaS app will launch its own AI agent feature. We are about to witness a massive acceleration in the proliferation of NHIs.
In this article, we examine the impact of AI agents on NHI security, explore emerging authentication methods, and offer our recommendations for the future.
Identity’s Blind Spot: Non-Human Identities
IAM systems ensure that only the right people – or machines – have access to the right enterprise resources, for the right reasons. However, not all identities are alike. The need to access data and make changes to core infrastructure makes machines, or non-humans, a complex and risky area of IAM.

NHIs are digital representations of these non-human entities and includeapplications, services, APIs, virtual machines, containers, bots, and IoT devices. NHIs enable secure machine-to-machine communication. In this context, the identity refers to the non-human entity registered in an IAM system, while the associated digital credentials (often called secrets) verify that identity. These digital credentials can take the form of certificates, tokens, or keys.
API keys are among the most recognizable NHIs, but their static nature carries security risks. OAuth tokens are likely the most prevalent, and users will recognize their fine-grained authorization when granting services access to view Gmail account details for single-sign-on purposes. However, OAuth tokens are also susceptible to theft and hijacking and they can be challenging to manage in distributed systems – since their expiration times are fixed at creation, revocation across widespread systems becomes difficult. Certificates provide the most robust security but require costly and complex management infrastructure. As a result of these trade-offs, the industry has standardized on using OAuth tokens for most use cases, and the security risks that this presents are critical for understanding the deeper issues posed by NHIs for identity security.

Consider the following example: a user approves access for a project management app to read their contacts from their core productivity suite (likely Microsoft 365). The flow is relatively simple and ubiquitous across many apps, highlighting the innovation that the OAuth standard has brought to the identity market. However, note that in this example (as in many real-world cases) the token is valid until manually revoked.

Because tokens and other authentication mechanisms require manual revocation, proper NHI lifecycle management is essential, yet is rarely implemented. As noted in our previous article, the lack of proper lifecycle management is just one of many pain points faced by those trying to secure NHIs. Additional issues include poor secrets management, over-permissioned access, secret sprawl, and the inability of NHIs to adhere to human-centric security measures. Unsurprisingly, hackers are increasingly exploiting these vulnerabilities – nearly one in five organizations has experienced an NHI-related security incident. Some of the world’s most renowned software enterprises, including Dropbox, Cloudflare and Microsoft, have not been immune to such incidents.
In the case of Microsoft’s attack by an alleged Russian state-sponsored actor known as Midnight Blizzard, attackers were able to leverage an NHI – a legacy OAuth test application – to gain access to Microsoft’s IT environment. Because the account possessed excessive privileges, the attackers were able to create new applications and user roles, move laterally within Microsoft’s IT environment, and eventually access Microsoft employee emails. While the details are technical, the key takeaway is clear: NHIs are over-permissioned and lack MFA, visibility and oversight, as well as proper lifecycle management for timely deprovisioning.

Adequately securing NHIs is one of the biggest, if not the biggest, challenge in identity security today – only 25% of organizations believe that they can prevent an NHI-based attack. We’ve said before that identity is the fundamental flaw in cybersecurity, and NHIs are the Achilles’ heel in this space. The most critical consideration of all is that we find ourselves in this situation before the inclusion of AI agents in our IT landscapes…